Difficult: Medium
Category: Mobile
OS: iOS
Description: Secure coding is the keystone of the application security!
After downloading the compressed file and decompressing it, we will have a folder where inside we find the files we need:
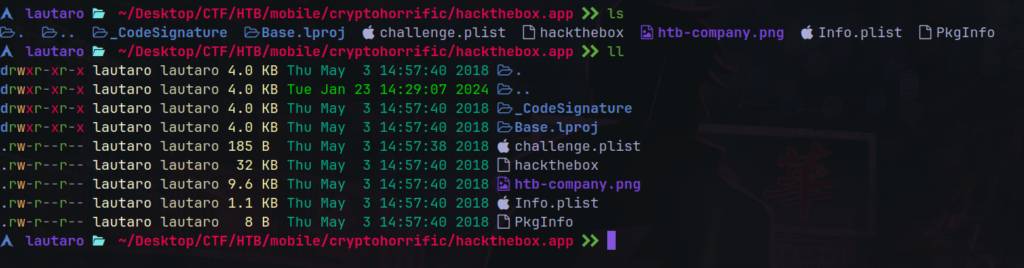
The hackthebox file, is the main file of the program that contains the binary files.
The .plist file is a list that contains details about the app and author.
This is for gather information when you search an App in the App Store.
The challenge.plist have some interesting:
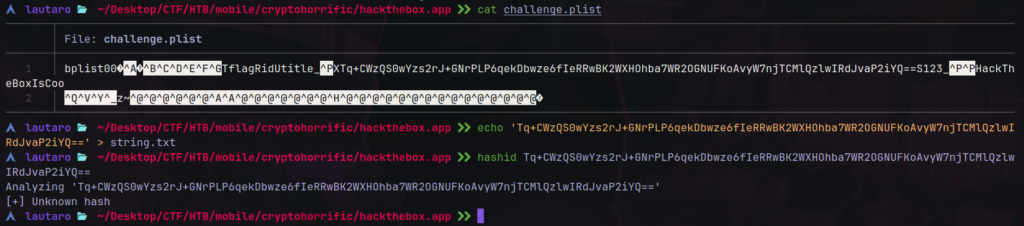
This must be an base64 encrypted text.
Tq+CWzQS0wYzs2rJ+GNrPLP6qekDbwze6fIeRRwBK2WXHOhba7WR2OGNUFKoAvyW7njTCMlQzlwIRdJvaP2iYQ==
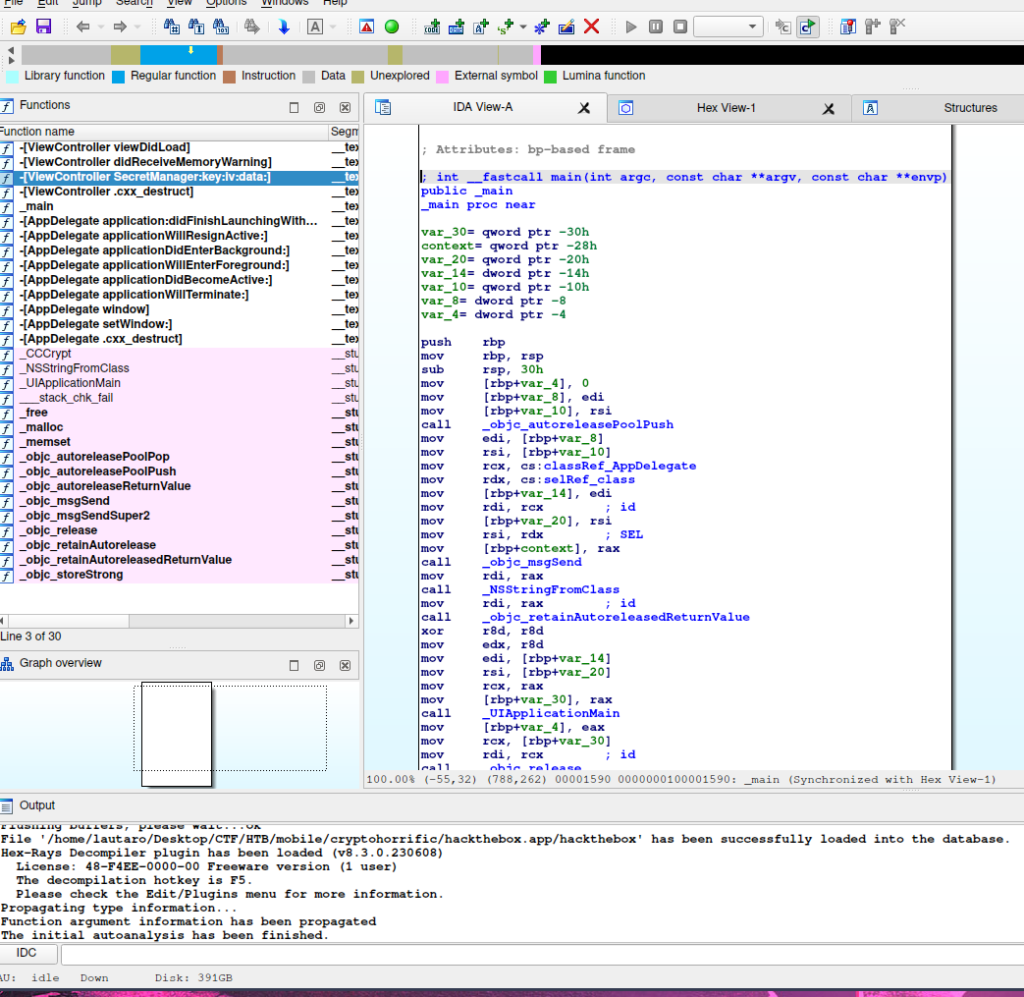
We load the hackthebox program to our IDA and let’s inspect that.
Here we have a insteresting function: _CCCrypt
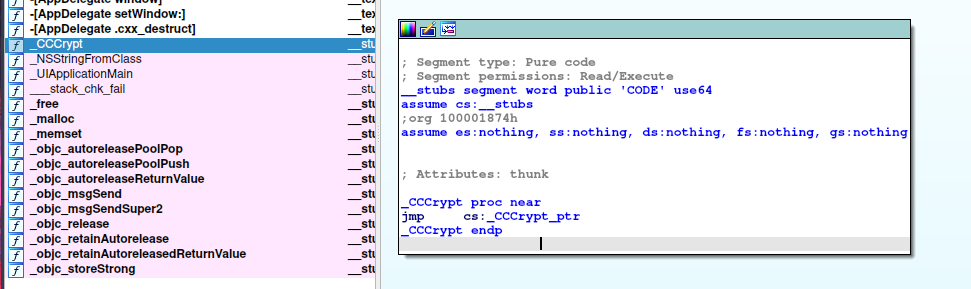
Following to CCCrypt_ptr we can see that jmp. So, navigate to CCCrypt_ptr and:
We can see between __cfstring some interesting things:
__cfstring:0000000100003128 dq offset aFlag ; "flag”
__cfstring:0000000100003108 dq offset aPlist ; "plist”
__cfstring:00000001000030E8 dq offset aChallenge ; "challenge”
__cfstring:00000001000030C8 dq offset aQftjwnzq4t7wZC ; "QfTjWnZq4t7w!z%C”
__cfstring:00000001000030A8 dq offset aADGKapdsgvky ; "!A%D*G-KaPdSgVkY”
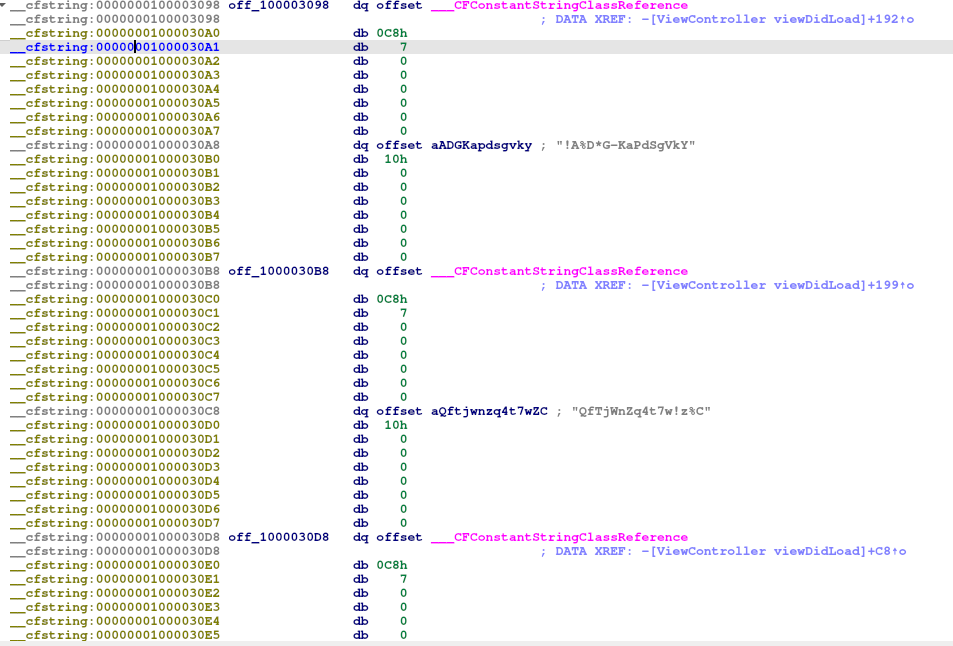
Following, for example: aADGKapdsgvky
We are redirect to:
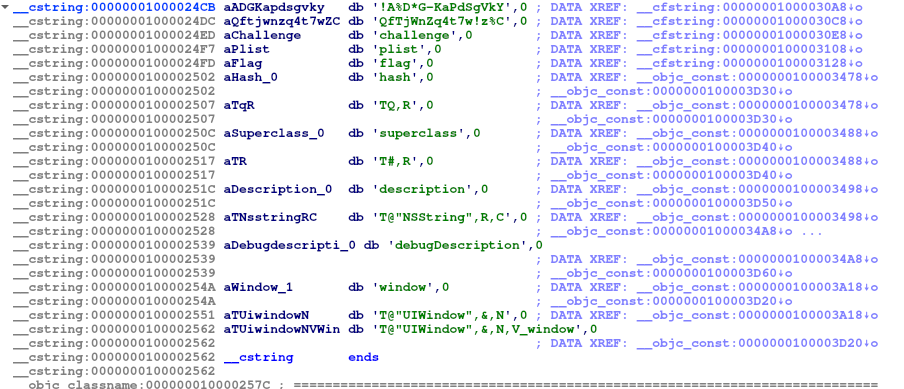
And may be this is the key and IV of an AES encryption. Let’s check:
!A%D*G-KaPdSgVkY
Tq+CWzQS0wYzs2rJ+GNrPLP6qekDbwze6fIeRRwBK2WXHOhba7WR2OGNUFKoAvyW7njTCMlQzlwIRdJvaP2iYQ==
So with these values, we can go to this online tool for decrypt:
https://www.devglan.com/online-tools/aes-encryption-decryption
And here is, the flag:
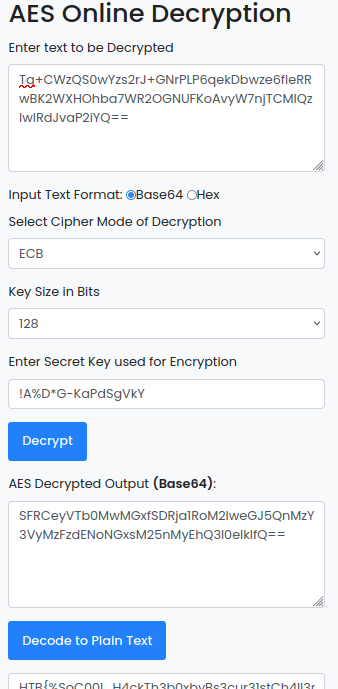
Decode to Plain Text and you will get the flag.
I hope you found it useful (:
Leave a Reply